AppOmni Shadow SaaS & Discovery
Client
AppOmni
Services
UX/UI Design, UX Research, Program Management
Timeline
6 months
Year
2024
Project Overview
Shadow SaaS, also referred to as SaaS Discovery, was a completely net-new feature that I led from inception through launch at AppOmni. The core challenge was simple but urgent: how could we claim to secure our customers' SaaS environments if we had no visibility into the unsanctioned applications employees were using? This gap, frequently cited in competitive losses, was critical to address, especially as we worked to expand into the mid-market space.
Motivation
Over the two quarters leading up to this initiative, AppOmni experienced roughly $8 million in competitive losses where lack of Shadow IT detection was a deciding factor. Customers, especially in the mid-market, were looking for a holistic view of their SaaS environment, not just protection for the apps they already knew about. We needed to deliver a solution that surfaced "unknown unknowns" in a way that was technically feasible, minimally invasive, and easy to act on.
Research
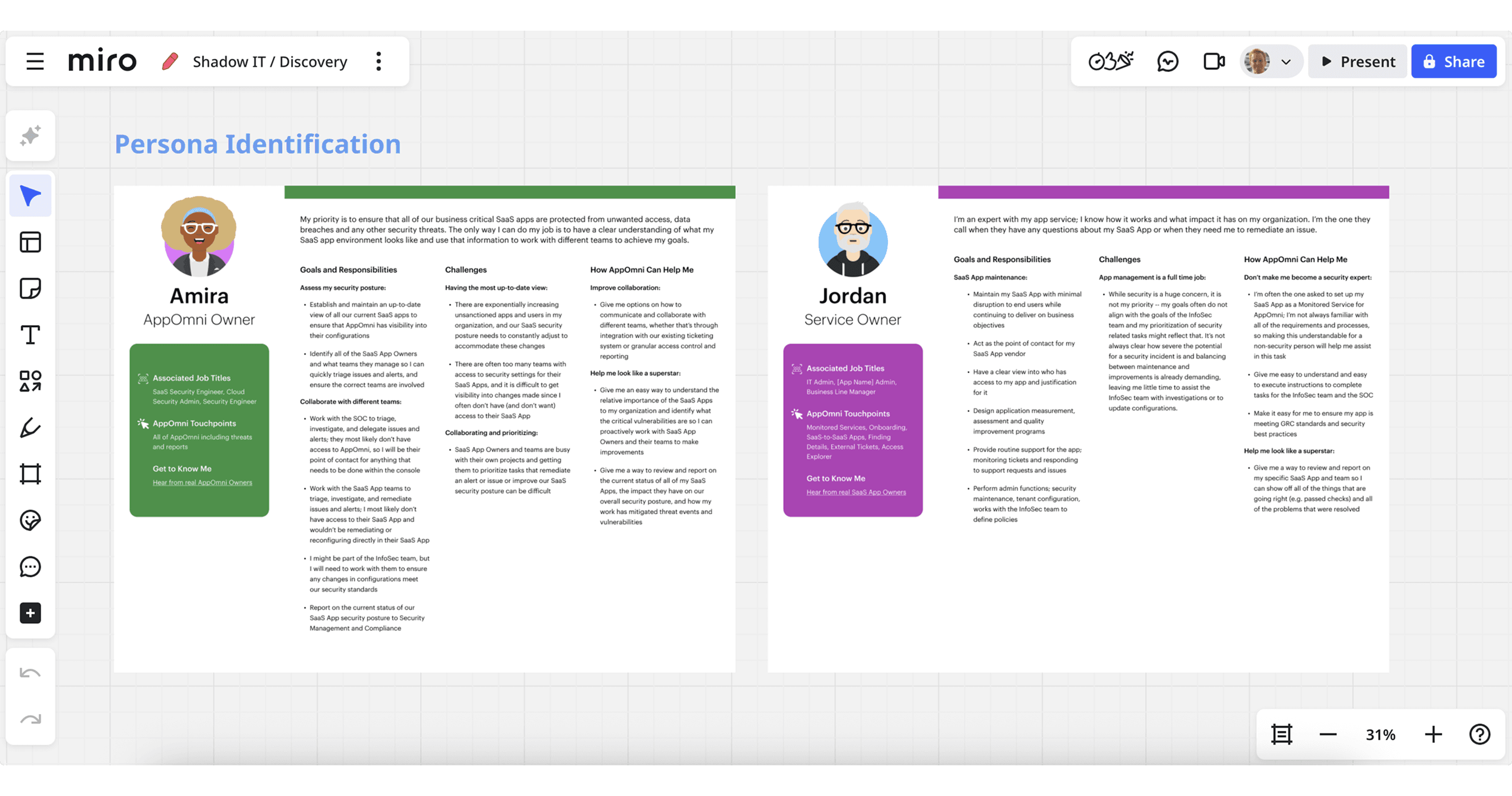
We spent over three months in deep discovery to make sure we built the right thing, the right way. I led a broad and rigorous research initiative that included:
Surveys with current customers and prospects to gauge interest, urgency, and perceived barriers
Nearly ~25 one-on-one interviews with:
Existing AppOmni customers
Potential customers evaluating our platform
Security professionals outside our pipeline for unbiased perspectives
Internal stakeholder workshops with Sales, Customer Success, and Solutions Engineering to capture anecdotal patterns and unmet needs
Competitive audits to understand how rivals positioned similar features, what resonated, and where their UX fell short
Our goals were to:
Clearly define the problem space from the customer’s perspective
Understand what “good” looked like in terms of data, context, and trust
Uncover any deal-breakers (e.g., privacy or implementation friction)
This research shaped the technical scope, product messaging, and interaction model from the outset.
Ideation
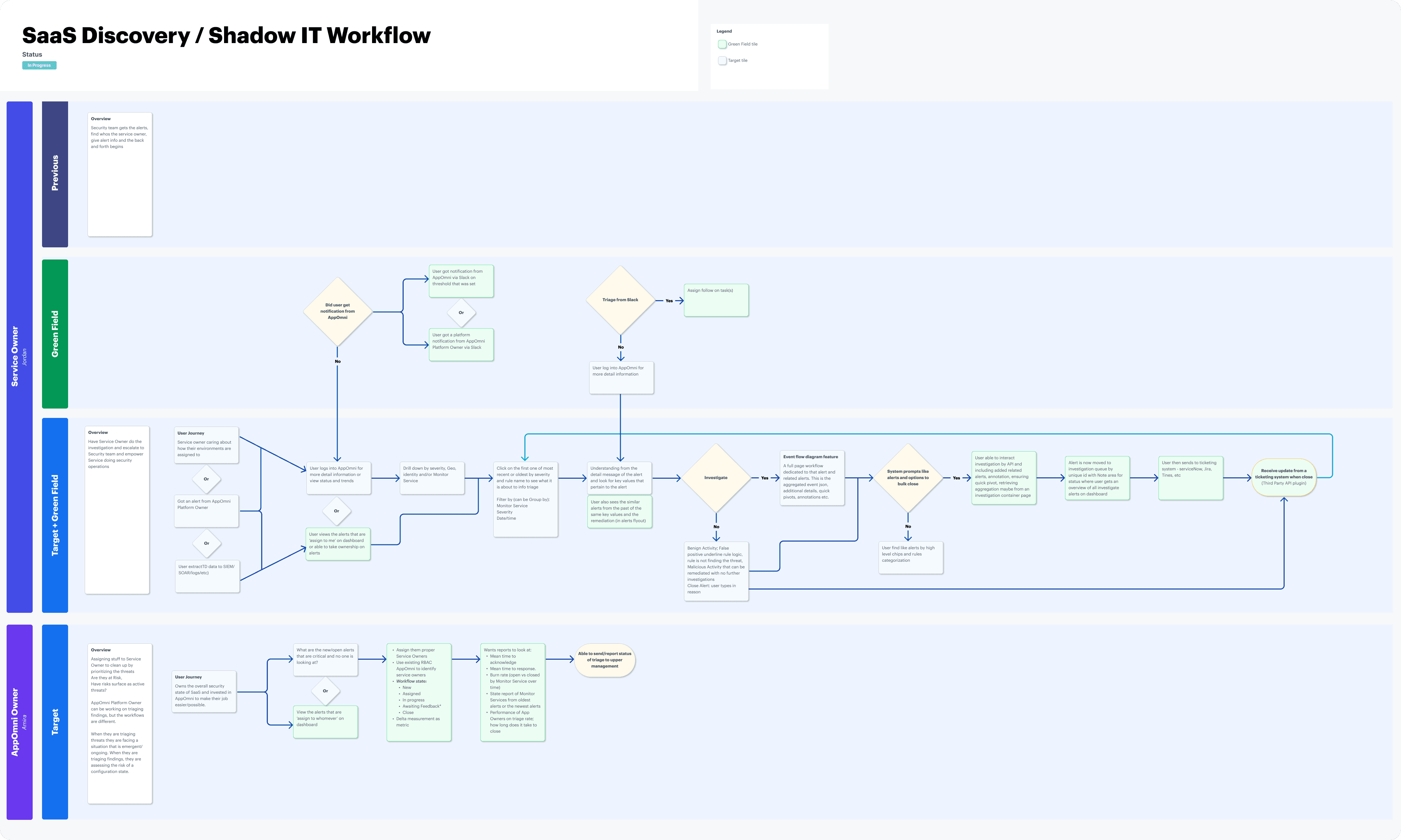
With a strong understanding of user needs and constraints, we began ideating. I led several co-design sessions with Engineering and Product to explore:
Detection strategies (e.g. traffic patterns, SSO mismatches, endpoint logs)
Alerting mechanisms (push vs pull, risk thresholds)
User context needs (who accessed the app, when, from where)
My UX role here went far beyond layout. I facilitated discussions that shaped the core product logic. One of the biggest challenges was aligning on a data ingestion strategy that balanced:
Technical feasibility: What sources could reliably provide indicators of Shadow IT?
Customer effort: Would the implementation require complex setup or elevated permissions?
Privacy expectations: Could we avoid triggering privacy concerns, especially for employee monitoring?
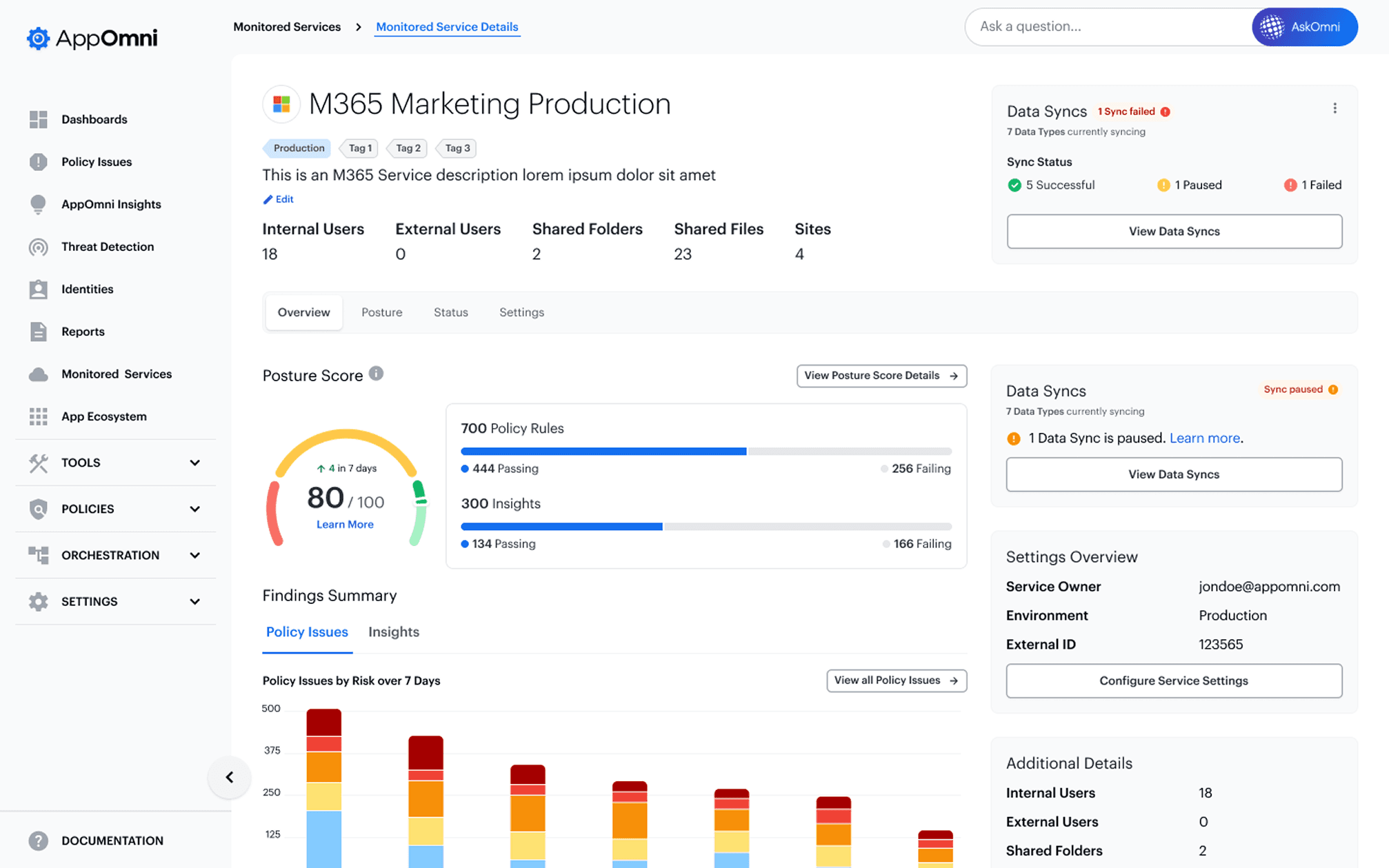
I sketched multiple models for how data could be presented: from flat lists of discovered apps to more dynamic, context-aware views that grouped usage by risk level or user type.
As we refined ideas, a clear need emerged: this feature could not live in isolation. It had to integrate cleanly into the broader AppOmni platform, particularly with Identities, to give customers rich, actionable context.
Prototyping
After locking in key design directions, I created a series of progressively refined prototypes, starting with low-fidelity flows and evolving into high-fidelity clickable prototypes in Figma.
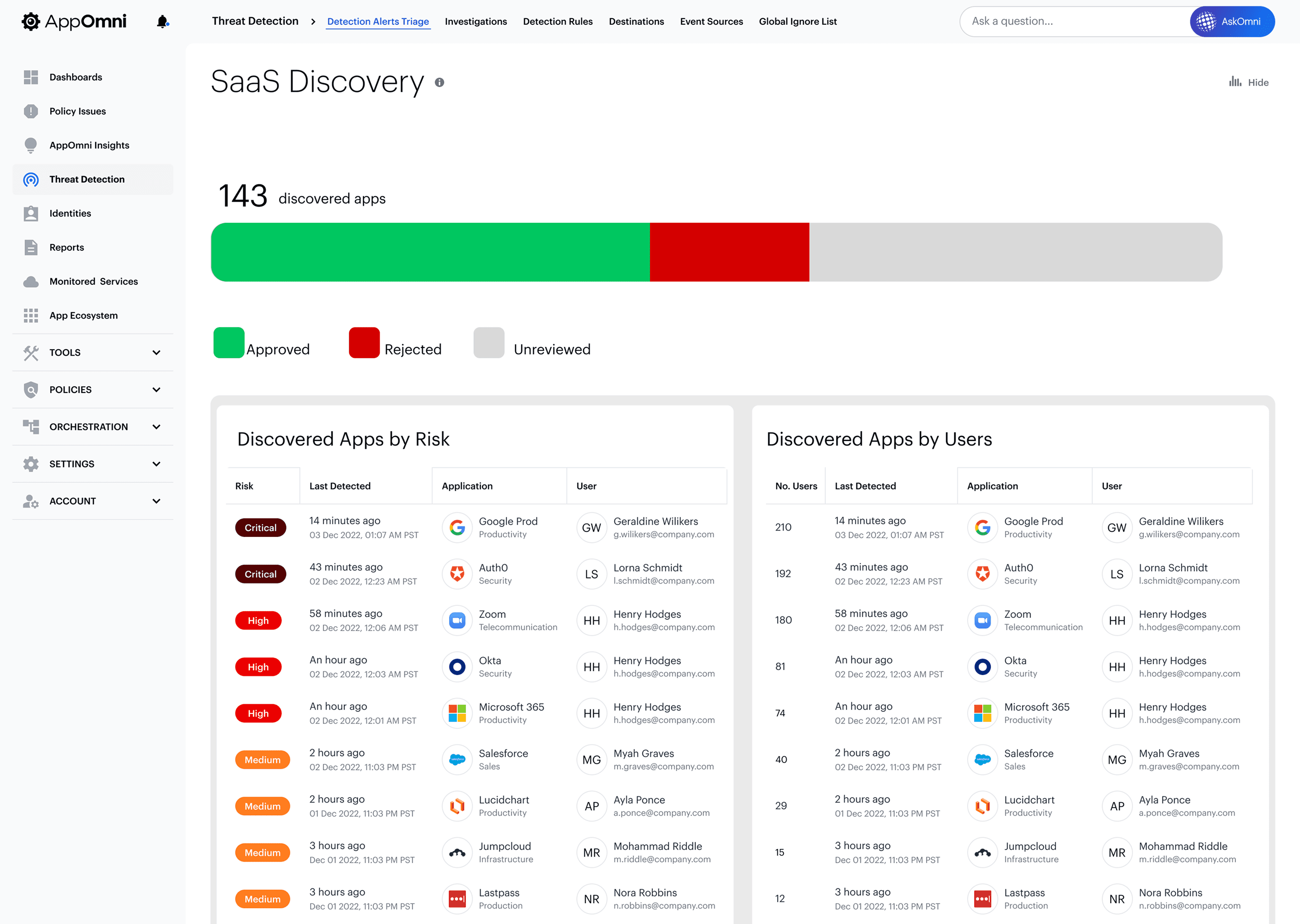
Each prototype explored variations of:
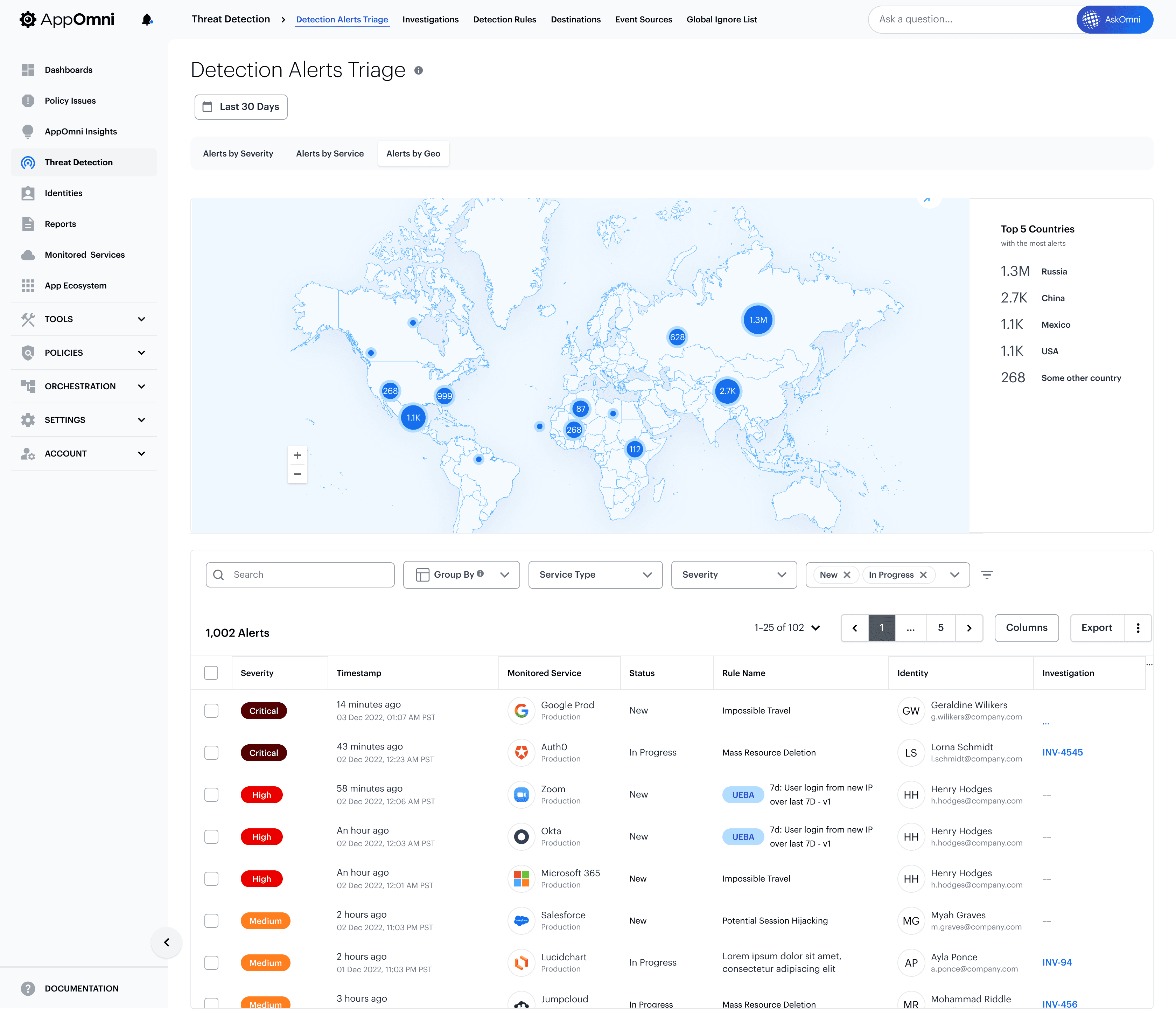
Discovery dashboards (by app, by user, by department)
Alert cards and timeline views
Next-action affordances (e.g. "block app", "request access review", "add to allowlist")
Prototypes emphasized clarity and call to action, avoiding “informational dead ends.” One of the early challenges was ensuring that each app discovery led somewhere; users needed to immediately understand what they were looking at, why it mattered, and what to do next.
I also built in interaction flows that connected Shadow IT alerts to the Identities feature, showing which user had accessed which app, and from what IP/device. This prototype interaction was critical for selling the vision internally and externally.
Testing & Iteration
We didn't treat validation as a one-off milestone, it was embedded throughout. I ran multiple rounds of moderated testing with:
Existing customers with mature security programs
Prospective buyers in evaluation
Internal stakeholders in Sales and Customer Success
We tested:
Comprehension of discovered app data
Clarity of user-specific access information (via Identities)
Effectiveness of proposed actions (e.g. alert triage, access reviews)
Key insights that drove iteration:
Customers didn’t always grasp what made a given app risky. We improved this by adding contextual tags and confidence indicators
Users wanted alerts to surface urgent issues, not just volume—so we added dynamic severity scoring
The first prototype lacked a strong “so what.” We reworked it to start with the consequence, not the activity (e.g. "5 users accessed Box from unmanaged devices.")
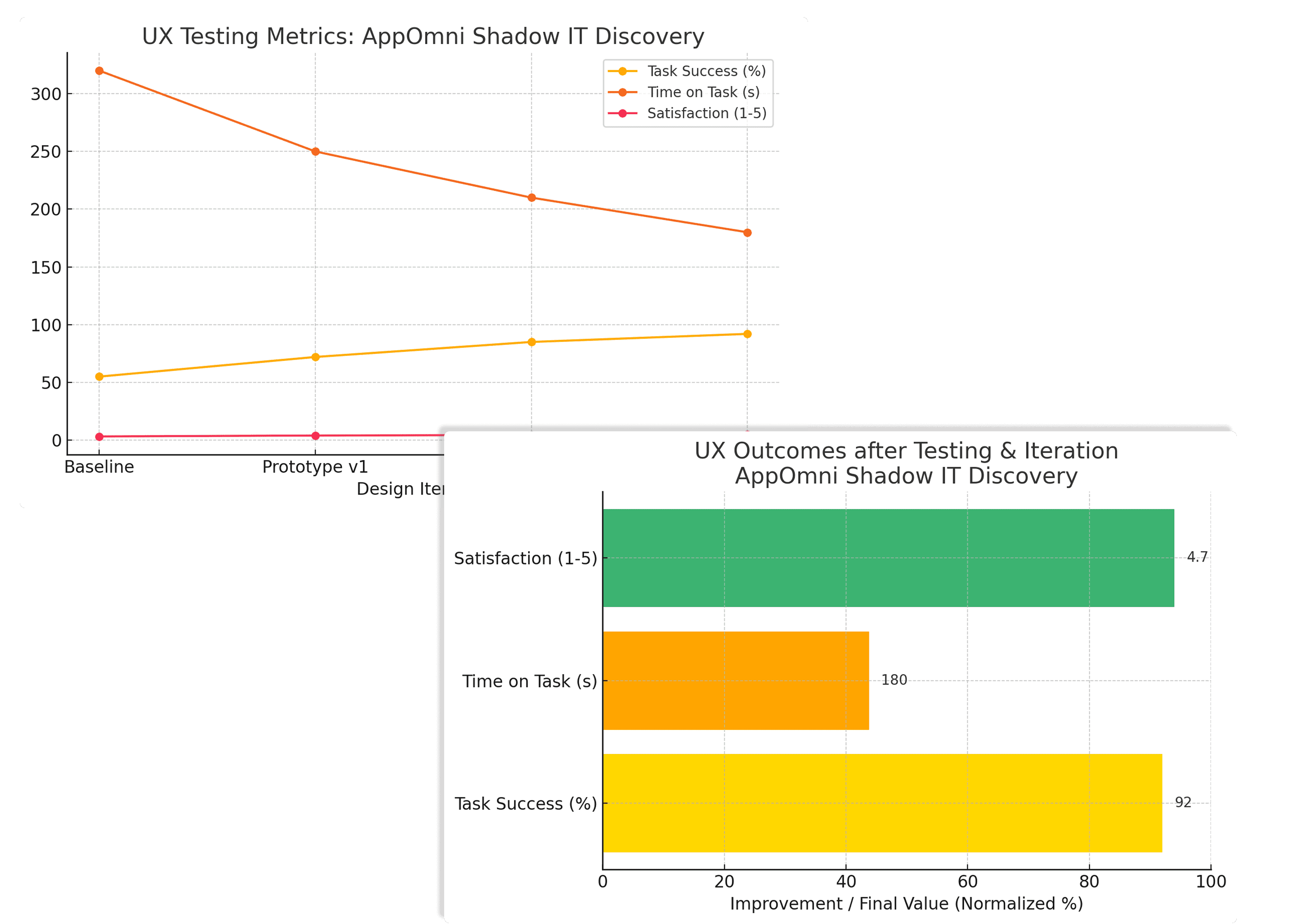
The feedback loop with Engineering was continuous, allowing us to validate technical feasibility in parallel with design usability. Every iteration brought us closer to a model that felt intuitive, contextual, and actionable.
Results & Takeaways
Shadow IT launched as a core feature of AppOmni and drove immediate impact:
Satisfaction around SaaS visibility rose ~25%, based on post-launch NPS and targeted follow-up surveys
Within the first quarter, the feature was a stated factor in over $4M in closed/won business, especially among mid-market prospects where we’d previously struggled
Multiple customers praised the tight integration with existing modules like Identities, which helped the feature feel native not bolted on
This project was a standout example of research-first design, cross-functional alignment, and the power of iteration. We succeeded not just by solving a problem, but by solving it in a way that aligned with customer values and our product’s long-term vision.